Alright, had some time to remember details of the SAKURA implementation of AES. Remember the objective of a ‘Hamming Distance’ model is to determine how many bits change on some data line / data bus.
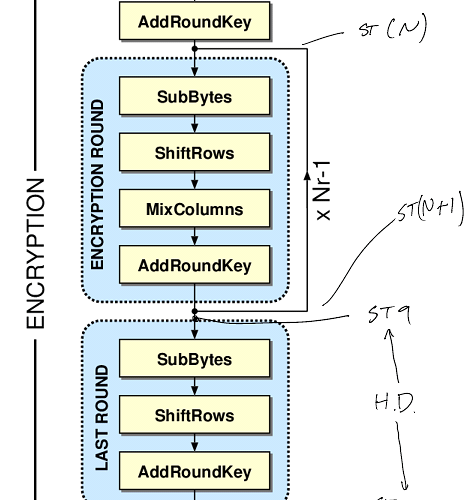
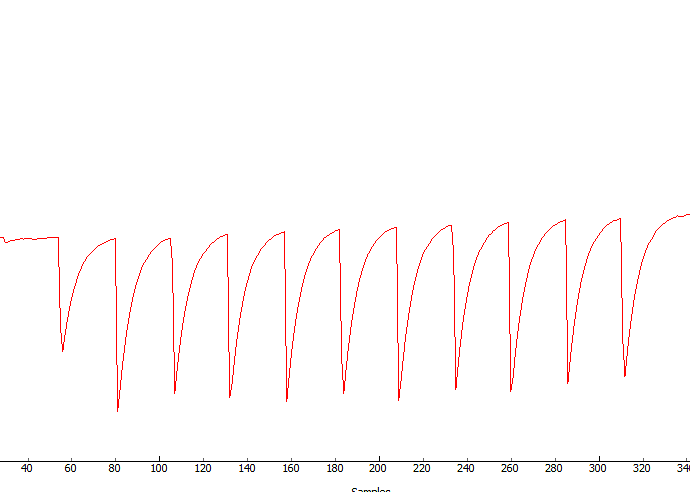
For the implementation used in the SAKURA-G (and I assume SAKURA-X too), it does an entire round in one clock cycle. What this means for you is that the only thing you can really do a ‘hamming distance’ attack against is the state, which will will call STN, where N is the round number. See the following figure:
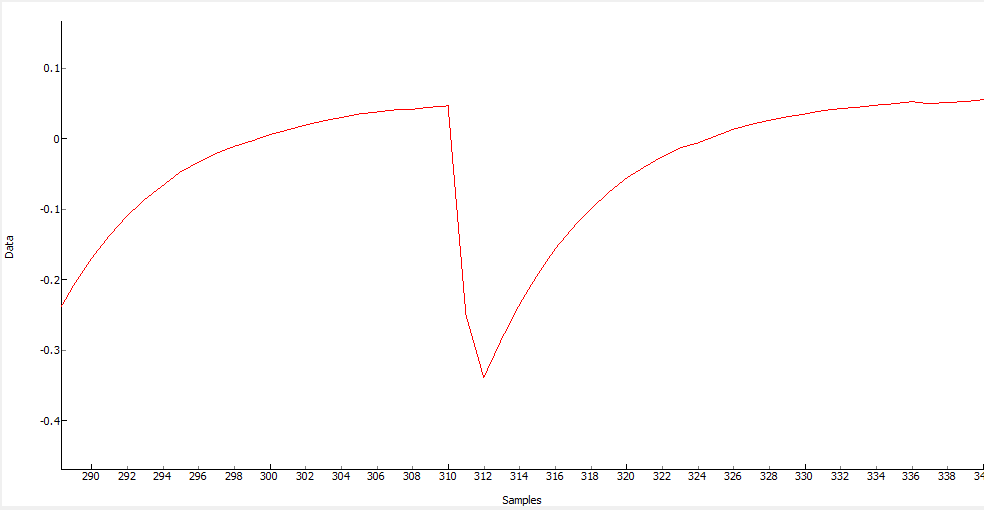
The classic HD attack on the SAKURA-G platform is actually using the cipher text. Thus what we are attacking is the difference between ST9 and ST10. The code in Python I’m using for this is as follows:
def HypHD(ct, key, bnum):
st10 = ct[INVSHIFT[bnum]]
st9 = aes_tables.i_sbox[ct[bnum] ^ key]
return getHW(st9 ^ st10)
The problem is you cannot do something similar with the input round due to the presence of mixcols. You have no way of testing how a single 8-bit sequence changed due to a different key guess. You CAN do this for the last round since it omits mixcols.
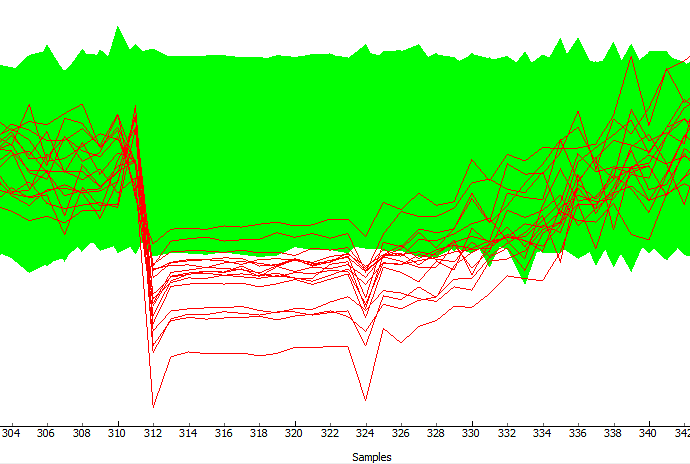
If you look at the FPGA source code, the only thing you can do easily do for the first-round attack is compare the PREVIOUS ciphertext to the new value of textin XOR keyguess. i.e. something like this:
def HypHD(pt, key, bnum, lastct):
st2 = pt[bnum] ^ key
st1 = lastct[bnum]
return getHW(st1 ^ st2)
This works since the FPGA holds the last valid state (i.e. the generated ciphertext) until it’s overwritten with the new plaintext XOR with the first-round key. The result is you can do the HD attack against the change in this state.
Hopefully this helps! Either way you’ll need to have recorded the ciphertext (i.e. output). If you don’t have that because your system doesn’t record it you can always cheat for testing purposes - i.e. you already know the input plaintext, you (presumably) know the encryption key, so just generate what the ciphertext should have been.
But I’d try to recreate the first attack and get that working before anything else.
 It’s always frustrating when you are starting out tracking down the issues…
It’s always frustrating when you are starting out tracking down the issues…