Hello, the success rate of attacking AES keys using the Attacking Acros MixColumns algorithm is not high. We hope to receive your help. Thank you very much.
The problem description is as follows:
Background: When using CW1173 devices to attack custom target versions of hardware AES keys, the success rate is only 20%. The design concept is as follows.
- Use 100MHz sampling to collect 25600 power consumption trajectory data for model building.
- Perform low-pass filtering and alignment processing on the collected power consumption trajectory data, with the alignment method based on the valley of the collected trajectory as a reference.
- Create a model using aligned trajectory data.
- Collect 256 power consumption trajectories for calculating keys, filter and align them, and use the created model to calculate the keys.
Question: - Do the collected power consumption trajectories need to undergo low-pass filtering and alignment processing? What are the effective filtering and alignment methods?
- Is it possible to use the valley of the trajectory as the alignment basis during the trajectory alignment process?
- Is the location of key leakage located near the valley of the collected trajectory
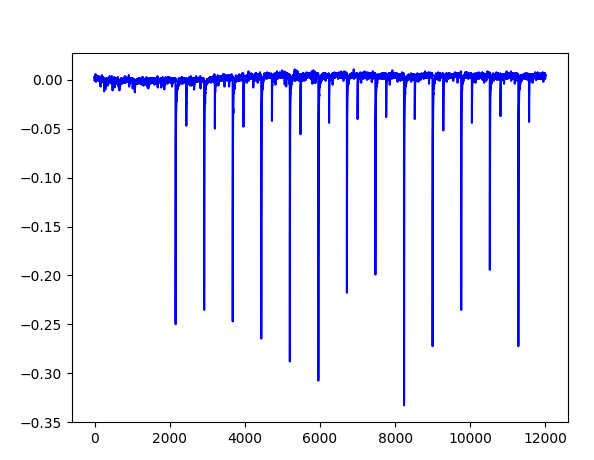
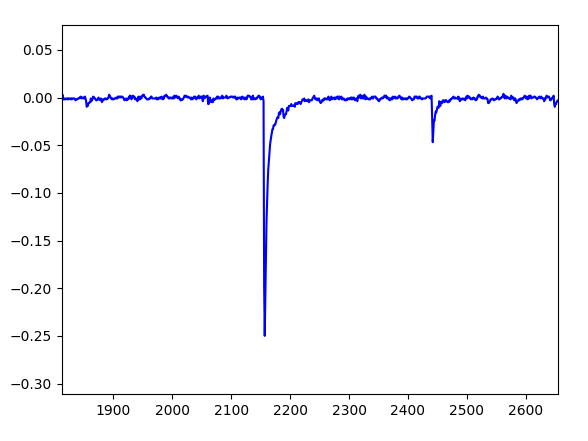
- Figure 1 shows the shape of a set of collected power consumption trajectories, with 13 valleys. Figure 2 shows the enlarged shape of a single valley position
- Which position in Figure 2 has the highest possibility of key leakage?
- What feature points can identify the location of key leakage in the collected trajectory?