Good afternoon,
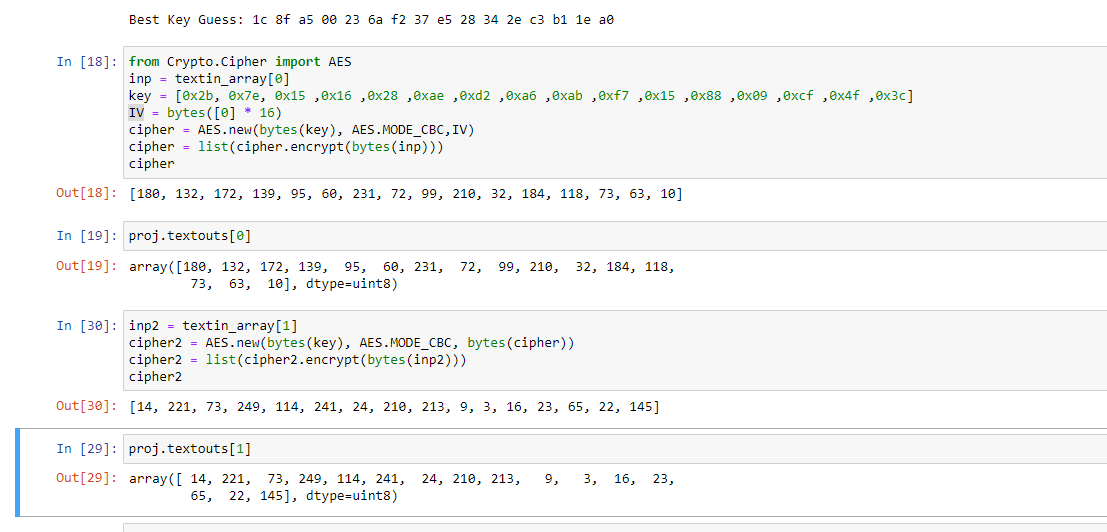
I am looking into attacking different modes of AES-128, and with this implementation, for some reason, I feel like I’m making a big mistake on the CBC mode, but I can’t seem to pinpoint where exactly. Any help is appreciated  . I can provide more information if needed (trace gathering code, explicit functions, etc)
. I can provide more information if needed (trace gathering code, explicit functions, etc)
t_bar = np.sum(trace_array, axis=0)/len(trace_array)
o_t = np.sqrt(np.sum((trace_array - t_bar)**2, axis=0))
cparefs = [0] * 16 # key byte guess correlations
bestguess = [0] * 16 # key byte guess
IV = [0] * 16
for bnum in tqdm(range(16)):
maxcpa = [0] * 256
for kguess in range(256):
if MODE == 'CBC':
hws = np.empty([len(textin_array),1])
for i,textin in enumerate(textin_array):
if i == 0:
prevct = IV[bnum]
else:
precvt = textout_array[i-1][bnum]
hws[i] = HW[aes_internal(textin[bnum] ^ prevct, kguess)]
if MODE == 'ECB':
hws = np.empty([len(textin_array),1])
for i,textin in enumerate(textin_array):
hws[i] = HW[aes_internal(textin[bnum],kguess)]
hws_bar = mean(hws)
o_hws = std_dev(hws, hws_bar)
correlation = cov(trace_array, t_bar, hws, hws_bar)
cpaoutput = correlation/(o_t*o_hws)
maxcpa[kguess] = max(abs(cpaoutput))
bestguess[bnum] = np.argmax(maxcpa)
cparefs[bnum] = max(maxcpa)
When running this code I get the wrong key as the best guess. Unsure if its because of the wrong definition of the leakage model, or something else.