Few time ago I looked at the available CW 308 targets and noticed very interesting target based on the NXP LPC55S69. This board is interesting from the side channel analysis attack due to PUF (Physical Uncloneable Function) bound to the HW AES accelerator. NXP claims that PUF based AES key usage in HW is protected by the mask:
/*!
* @brief Reconstruct hw bus key from a key code
*
* The digital fingerprint generated during the Start operation and the KC
* generated during a Set Key operation (Set intrinsic key or Set user key) are used to retrieve a stored key. This
* operation needs to be done every time a key is needed.
* This function accepts only Key Codes created for PUF index register kPUF_KeyIndex_00.
* Such a key is output directly to a dedicated hardware bus. The reconstructed key is not exposed to system memory.
*
* @param base PUF peripheral base address
* @param keyCode Word aligned address of the input key code.
* @param keyCodeSize Size of the keyCode buffer in bytes. Shall be PUF_GET_KEY_CODE_SIZE_FOR_KEY_SIZE(keySize).
* @param keySlot key slot to output on hw bus. Parameter is ignored on devices with less than two key slots.
* @param keyMask key masking value. Shall be random for each POR/reset. Value does not have to be cryptographicaly
* secure.
* @return Status of get key operation.
*/
status_t PUF_GetHwKey(
PUF_Type *base, const uint8_t *keyCode, size_t keyCodeSize, puf_key_slot_t keySlot, uint32_t keyMask);
Another interesting features are secure boot, TrustZone M. So fault injection is a good choice to attack MPU, SAI, Secure AHB configuration to break HW domain isolation.
It worth to dump and reverse the BootROM. It has many security techniques to protect against the fault injection and tampering!
In my opinion, NXP board is much better than dealing with the STM32F based targets.
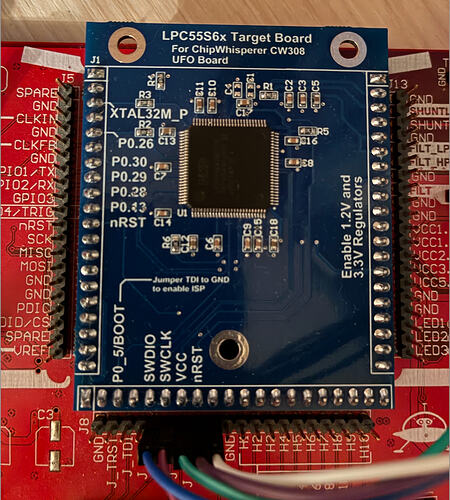
Unfortunately, for unknown reasons, NewAE doesn’t produce these targets so I decided to make it by myself.
The mistake I made, I blindly trust the standalone gerber project. It turned out it is outdated and out of sync with the Altium project. The gerber project is V2 project - the P0.13 PIN is open drain PIN with missed pull up resistor, connection to the feedback PIN is missed. To fix the first issue I just used neighbour P.0.28 routed to the GPIO3 (this output is used for triggering). To fix the second issue I shorted 44-45 pins.
Here is the sample I made at home:
Another one thing I would like to highlight, all LPC55S69 in the marked are 1B version(where fixed a bunch of BootROM issues). So if one will decide to build the SW, it just won’t work due to many broken things (wrong clock configuration, wrong pin configuration). But it is pretty easy to fix. Also I increased the UART speed from 38400 to 115200.
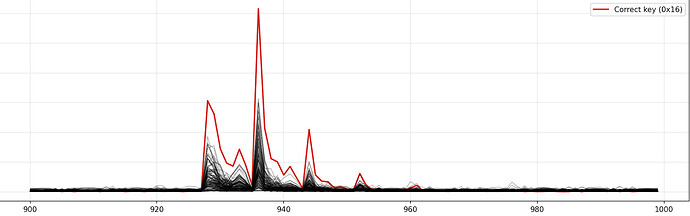
As a result I was able to recover both AES-128 and AES-256 keys from the HW crypto.
with 30000 power traces 14 bytes are clearly recovered. 8-th and 16-th key bytes are noisy. Increasing the power traces up to 100K makes possible to recover the whole key.
It worth to say, the Pearson correlation works bad here and I use my own approach.
The most interesting thing is masked AES. Surprisingly, the mask doesn’t affect key recovery at all. This is a question to NXP (what is the purpose of this mask if it doesn’t protect passing it explicitly via PUF_GetHwKey()).
So, I can say, it is definitely worth to try this target! You will learn a lot of things.