For the RSA chipwhisperer tutorial, the RSA algorithm successfully flashed onto the STM32F3 but there is no textout being returned.
It says WARNING - Timeout in OpenADC capture(), trigger FORCED.
How do I fix this?
For the RSA chipwhisperer tutorial, the RSA algorithm successfully flashed onto the STM32F3 but there is no textout being returned.
It says WARNING - Timeout in OpenADC capture(), trigger FORCED.
How do I fix this?
Hi Andrew,
I would first check the usual suspects: is the ADC locked? Is the target clock correctly set? Is the UART rate set correctly?
Jean-Pierre
Hi Jean-Pierre,
thanks for the quick reply. Doesn’t the STM32F, RSA setup script which I ran do these things already?
Andrew
Yes it does, but sometimes the DCMs fail to lock. It’s always a good idea to check that when running into unexpected behaviour.
I checked those three things you mentioned but it still does not work. No output is being returned on the encryption status monitor when I click capture.
If you send a “v” command using the terminal tool, do you get a “z00” response?
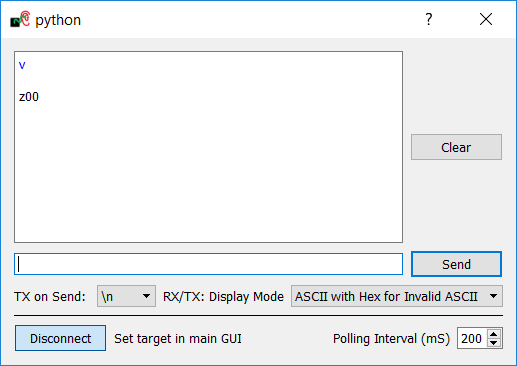
Yes when I enter v, I get z00
Just to be sure, did you follow step 2 in the tutorial?
BTW it’s normal that you’re not getting anything back on the encryption status monitor. If you look at the firmware source in simpleserial-arm, you’ll see that there are no calls to simpleserial_put.
From your screen capture it’s evident that the target is doing something. Unfortunately I don’t have an STM32 target to confirm, but I have a feeling that what may be happening is that in simpleserial-rsa-arm.c, the “goto cleanup” happens, which skips over the trigger generation, which would explain your timeout… quick test to confirm, move the trigger_high/low somewhere it will always execute?
Step 2 as in the hardware setup? I think I did that since AES worked properly.
Sorry what do you mean “move the trigger_high/low somewhere it will always execute?”
This is what the terminal looks like when I try to run.
Sorry I wasn’t clear; I meant this step 2 under “Finding SPA Leakage”:
Under the Target Settings tab, leave only the “Go Command”, and delete the other commands (Load Key and Output Format). The RSA demo does not support sending a key, and instead will use the plaintext as a fake-key.
In hardware/victims/firmware/simpleserial-rsa/simpleserial-rsa-arm.c, line 199 in the get_pt function, you find:
trigger_high();
MBEDTLS_MPI_CHK( mbedtls_mpi_exp_mod( &T1, &T, &fake_DP, &rsa_ctx.P, &rsa_ctx.RP ) );
trigger_low();
Remove those trigger_high() and trigger_low() calls, and insert this before the MBEDTLS_MPI_CHK call on line 180:
trigger_high();
trigger_low();
as an experiment to confirm whether the mbedtls_mpi_cmp_mpi() call is the reason why the CW capture is timing out. This won’t solve anything but it may give a clue as to what’s happening.
The timeout error is gone now.
RSA seems to run and I got a power trace that looks like this, but the power trace is different from the one displayed on the tutorial. What is the problem here?
Thanks for reporting back. So if you follow the code in simpleserial-rsa-arm.c, this confims that the “goto cleanup” is being taken due to the error code from mbedtls_mpi_cmp_mpi().
I don’t have an STM32 target yet but I will soon; when I do I’ll be able to investigate further.
Thanks for you patience…
Hi Andrew,
Unfortunately, this tutorial cannot be completed on any target but the XMega. There were plans to port the tutorial to the Arm targets as well, but all of the libraries that we’ve examined for Arm targets use a different method of multiplying integers (which is what we’re attacking here), making the attack much weaker and a bit more complicated.
Sorry about the late response,
Alex
An update on the RSA tutorial: CW5 now has a new RSA attack that uses fault injection to break RSA signatures.