Hi
We are going to perform a CPA on an AES-256 with a CTR( Counter) mode. Our problem is that we have a hard time getting this all set up. Our PLATFORM= “CW308_STM32F3”, and somebody told us that the CTR mode were in CRYPTO_TARGET = “MBEDTLS”. Is there an easy way to switch to AES- 256 and mode to CTR, or do we have to make our own SimpleSeries, if so how is this done?
Thanks in advance
Two summer interns who are struggling
Hi,
You’ll need to do the following:
- Change the length of the
'k' command from 16 bytes to 32 bytes in the simpleserial_addcmd() for get_key().
- Change
get_key() to use a 32 byte key instead of a 16 byte key
- Change
get_pt() to use mbedtls_aes_crypt_ctr()
I’d recommend taking a look at firmware/crypto/aes-independent.c. You can find mbedtls in firmware/crypto/mbedtls.
Hope that helps,
Alex
1 Like
Hi again,
Thank you for your answer. However I am stuck trying to use a 32 byte key instead of a 16 byte key in get_key(). Can you (or anybody else) tell us what to exactly change?
uint8_t get_key(uint8_t* k, uint8_t len)
{ aes_indep_key(k);
return 0x00;
}
Also why do we not need to change " static uint16_t num_encryption_rounds = 10; " to " = 14 " since we are changing from AES-128 to AES-256?
We are modifying simpleserial-aes.c, is this the correct file to change?
Again thanks for the help
Yup, you’re modifying simpleserial-aes.c. There’s no need to modify num_encryption_rounds, as that’s for doing many full encryptions.
Try including “aes.h” (should get automatically pulled in from mbedtls) and directly using the functions from mbedtls.
Alex
Thx again, but what about the first part of my question?
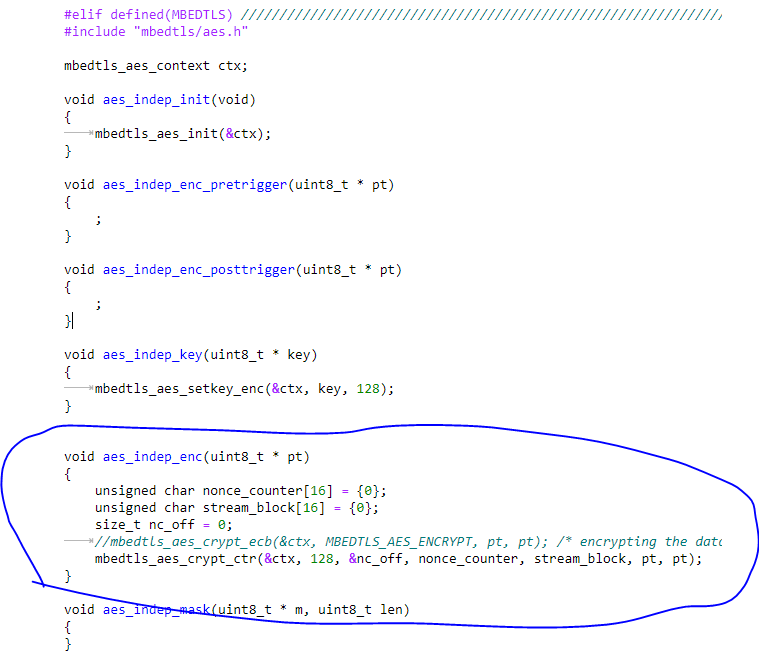
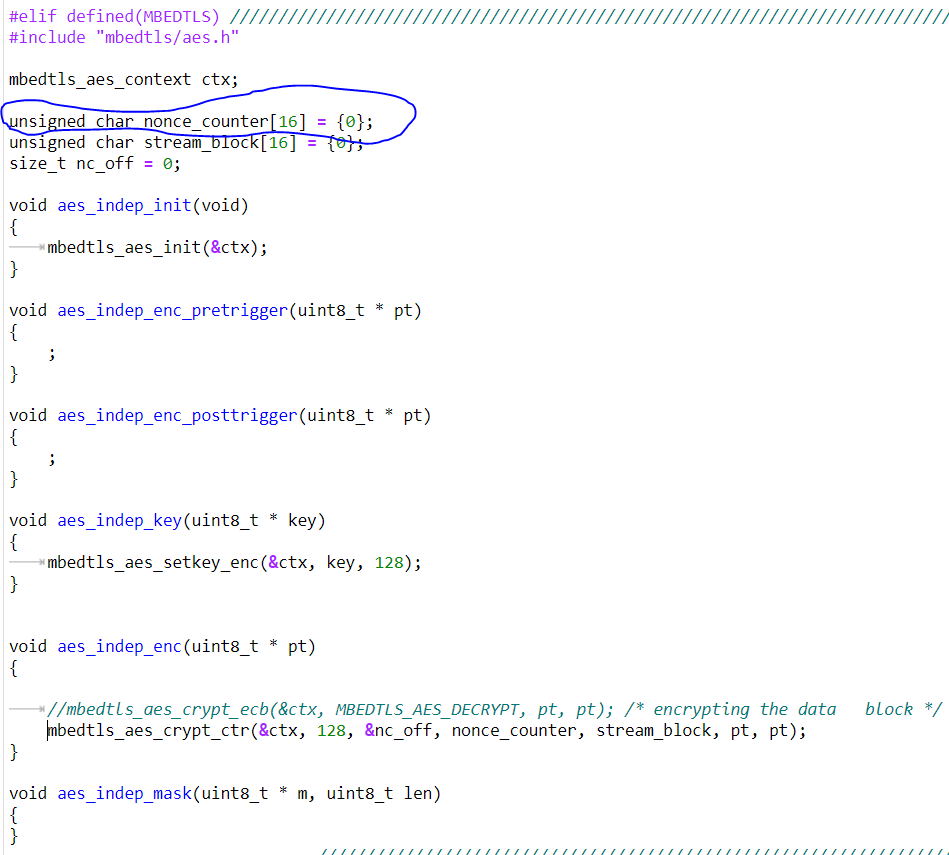
If you look at the mbedtls code we have:
You can see the mbedtls setkey function takes an argument that specifies how long the key is. I recommend using these mbedtls functions directly.
Alex
1 Like
Thank you for your help Alex 
One last thing; is there any of the tutorials we can manipulate slightly to be able to perform a CTR attack( if so, which one and what to change), or must we write it basically from scratch? If the latter is the case, do you have any tips of an pseudocode or articles that deals with the actual implementation?
Best regards
Yup, this should only require slight modifications from a regular attack. If we look at a block diagram for CTR mode:

we’ll either need the input to the block cipher (Nonce||Counter), or the output of the block cipher (Plaintext + Ciphertext). If you want to attack via the former, you can use the same model as the normal mbed attack and replace the plaintext with Nonce||Counter. If you want to attack the latter, IIRC the correct model is LastroundHW and you’ll want to use PT + CT as your ciphertext.
Hope that helps
2 Likes
Hey again Alex,
I want to attack via the input to the block cipher (Nonce||Counter), since this is known information in my case.
- So in summary I can just change the input from plain text to Nonce||Counter in for example “Lab 4_3 - ChipWhisperer Analyzer CPA Attack (MAIN)” and then the AES-128 CTR Mode will work?
’
- Exactly how to I change from plain text to Nonce||Counter? Like what function(s) and which parameters
’
- Is this correctly implemented?
’
’
’
In regards to changing to AES-256 CTR Mode (which is my final goal), from my understanding this would require more modification than you have previously shown, for example in the “Lab 3_1A - AES256 Bootloader Attack” for the CBC Mode, one must do two different steps in order to retrieve the full key. None of the other labs has this second step.
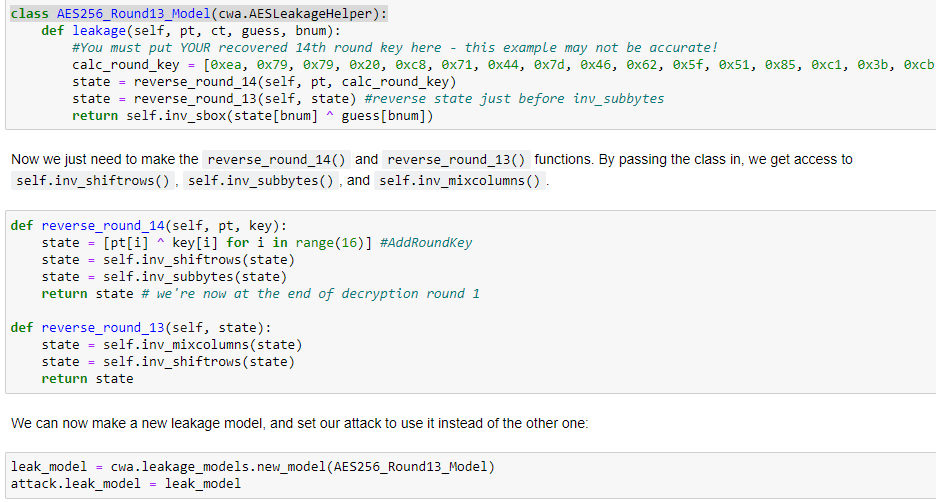
“Analyzer doesn’t have a leakage model for the 13th round key built in, so we’ll need to create our own. Let’s work through this now. To make a new model, we start off by inheriting the AESLeakageHelper class. We need to make a leakage() method that calculates the Hamming weight we use in the CPA attack.” - from Lab 3_1A - AES256 Bootloader Attack
’
- Do we need to make our own
leakage() method that calculates the Hamming weight we use in the CPA attack i.e make something similar to this? I have learned that the AES-128 CTR needs 4 round, while AES-256 needs 5 rounds, so I am guessing that I need to make 4/5 versions of this step?
Thank you so much for your help Alex, you have been a lifesaver 
So in summary I can just change the input from plain text to Nonce||Counter in for example “Lab 4_3 - ChipWhisperer Analyzer CPA Attack (MAIN)” and then the AES-128 CTR Mode will work?
Yup, that’s correct.
Exactly how to I change from plain text to Nonce||Counter? Like what function(s) and which parameters
When you add traces to your project, change textin to Nonce||Counter: Deprecated API — ChipWhisperer 5.7.0 documentation. You might need to break cw.capture_trace() into its components: see the implementation of capture_trace()
Is this correctly implemented?
You need to make nonce_counter, nc_off, and stream_block global variables, as they’re directly used by mbedtls and having them reset each time you enter aes_indep_enc() will cause the counter to never advance.
You should be able to get the first half of the key by using the standard attack, then advance Nonce||Counter through ARK, SubBytes, ShiftRows, and MixColumns. You can then use that to repeat the attack and get the second half of the key.
Happy to help 
Alex
Hey again,
I am trying to replicate a certain CTR AES-256 paper View of Recovering the CTR_DRBG state in 256 traces (iacr.org) View of Recovering the CTR_DRBG state in 256 traces (iacr.org), with this code AttackAESCTR/AES-CTR-attack.ipynb at master · LaurenDM/AttackAESCTR · GitHub, and as you can see, she made a very general approach(no built-in cw-functions) to what I desire which I can follow. However, she does not include how to obtain the traces being used, she just loads them in. I know she used ChipWhisperer so I should be able to reproduce her results.
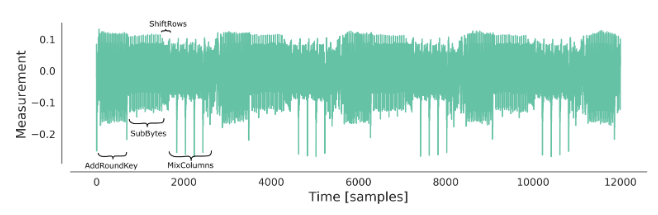
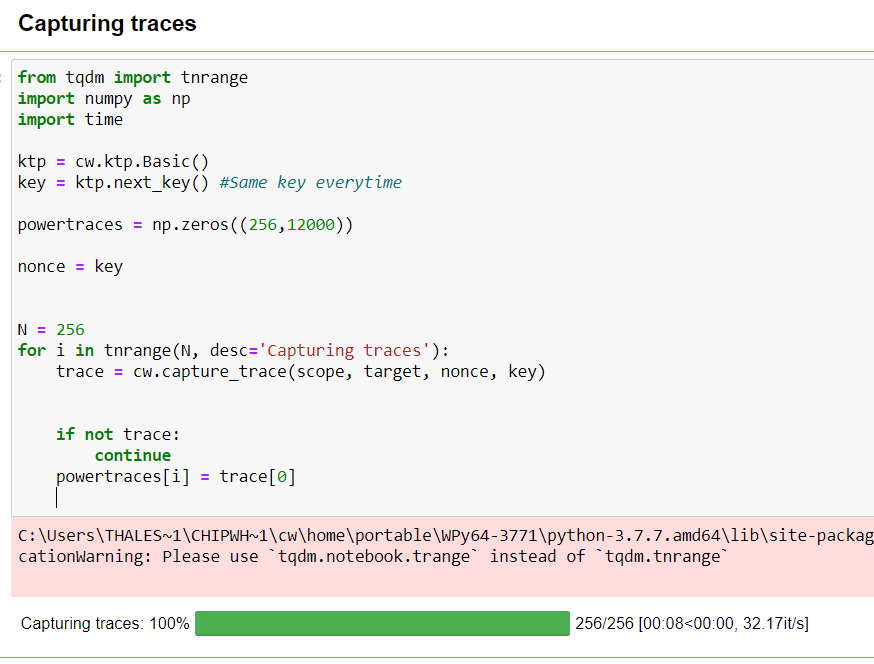
My end state is when I get traces on her format i.e.:
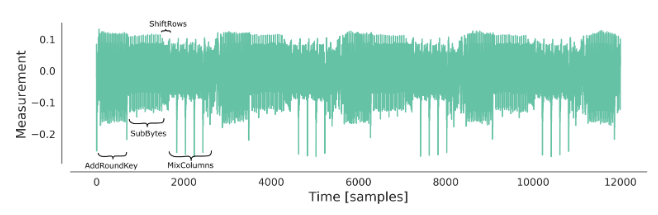
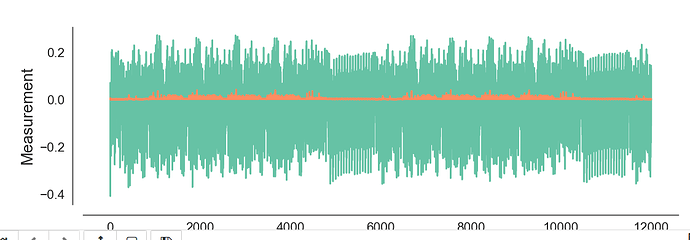
and so far I am at this(dont worry about the orange line, it is just the std ):
it looks like their is som “SubBytes” going on, but they are more spaced out, and there is no 4 visible spikes in “MixColumns”.
So my question is: How do I get the same graph?
My code is as follows:
As you can see I switched “text” with “nonce”, and just used the same as the key. But I do not get why you would want to switch out the input text. The nonce is defined in aes-independant.c, so should it not be sufficient to just use “text” in capture_trac()? (I tried both, and neither worked for me though)
Another small question I have is how to write the CW-arrays, i.e. CWbytearray(b’2b 7e 15 16 28 ae d2 a6 ab f7 15 88 09 cf 4f 3c’)? If I want to make my own, I have to use a for-loop and change the elements, is there a shorter way?
Again thx so much for the help Alex
Best regards
I think you’re comparing two different two different implementations of AES. That first plot looks like TINYAES128C, not MBEDTLS.
Another small question I have is how to write the CW-arrays, i.e. CWbytearray(b’2b 7e 15 16 28 ae d2 a6 ab f7 15 88 09 cf 4f 3c’)? If I want to make my own, I have to use a for-loop and change the elements, is there a shorter way?
The CWbytearrays are just a builtin Python bytearray with the string conversion method replaced so that its output looks a little nicer.
Alex
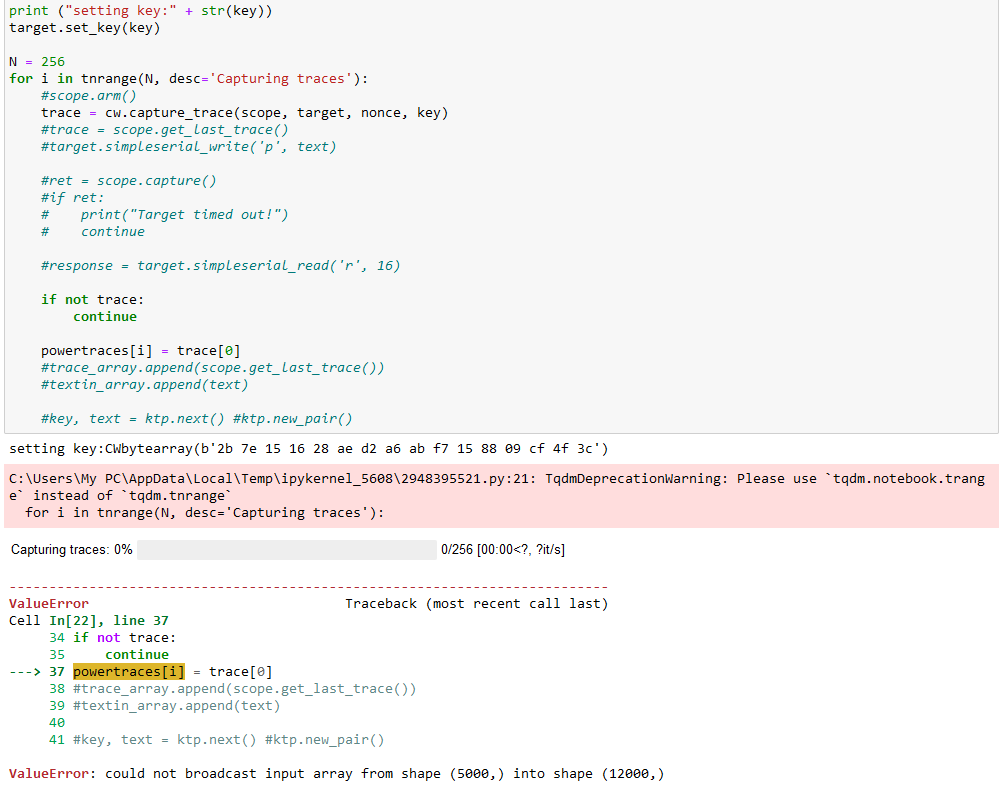
@sca_fanatic what setting have you done for scope, as I am running the same code and getting following error. Can you kindly guide me?
For Snow-V do I need to do these things.
Because after increasing 16 to 32, I’m getting an out of range error