For those who might find this interesting to see…
There is too little public information about side channel attacks against smart card’s HW AES. So, I decided to share some findings here.
The target smart card is pretty old NXP Jcop 2.4.1 card released in late 2000’s
The main benefit is ability to install own applet on the card and use Java crypto API. On runtime, the NXP’s JCVM invokes low level HW AES accelerator. It looks like a good target.
To sync encryption and power traces capturing, I use the edge count trigger to the well known APDU message which sends the plaintext to the card. On triggering the edge counter, the embedded logic analyzer starts counting the samples on the IO SC line to detect first start bit of the smart card reply. This helps me to locate the crypto interval (request - response) very precisely.
The next step is to locate the HW AES itself as the crypto interval is ~90K samples. I use such trick
for (short i = 0; i < (short) 10; i++) {
eepromMarker[i] = (byte) 0xAA;
}
aesCipher.doFinal(buffer, ISO7816.OFFSET_CDATA, (short) 16, buffer, (short) 0);
for (short i = 0; i < (short) 10; i++) {
eepromMarker[i] = (byte) 0x55;
}
to trigger heavy power consumption EEPROM write activity. This helped a lot me to identify the AES range quickly. As expected, AES was surrounded by sharp and deep spikes.
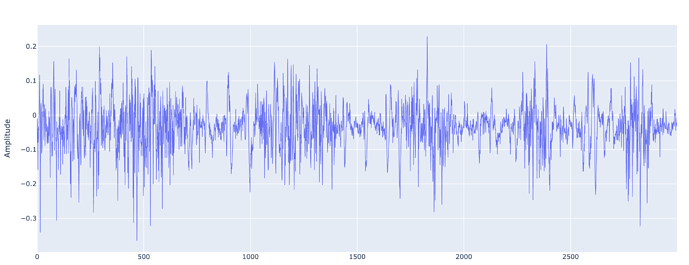
Here is the picture of aesCipher.doFinal(buffer, ISO7816.OFFSET_CDATA, (short) 16, buffer, (short) 0);
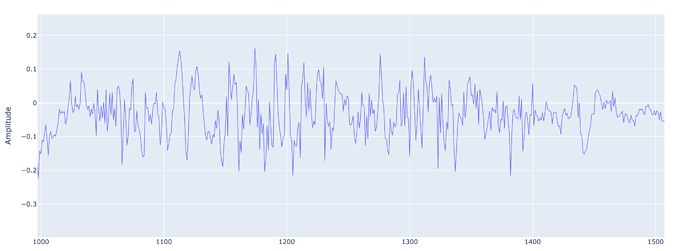
I am not sure what exactly happens here, in this zoom in picture. In my opinion it is very noisy trace.
Look at this noise hell
In my opinion, there are no chances to break through this noise.